Dynamic Analysis Using MobSF: A Beginner-Friendly Guide

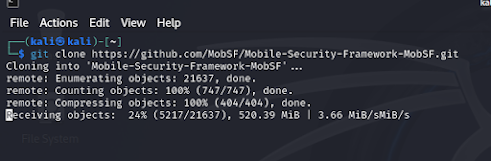
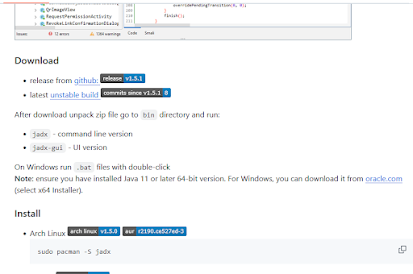
Dynamic Analysis of Spotify App on Genymotion Using MobSF: A Beginner-Friendly Guide Dynamic analysis is a powerful way to monitor how apps behave in real-time while they’re running. This guide will show you how to perform dynamic analysis on the Spotify application using Genymotion and MobSF (Mobile Security Framework) . Let’s break it down step by step so you can follow along, even if you’re new to mobile security testing. What is Dynamic Analysis? Dynamic analysis means running an app in a controlled environment to observe its behavior. For example, you might: Check how it interacts with a network. See if it’s leaking sensitive data like passwords. Monitor permissions and system calls it makes. By analyzing Spotify dynamically, we can understand its security behavior without looking into the code. Why Use MobSF? MobSF : A powerful tool that helps analyze the security of Android and iOS apps, offering both static (code-based) and dynamic analysis capabilities. Steps to Analyze...