What is Phone Jammer?
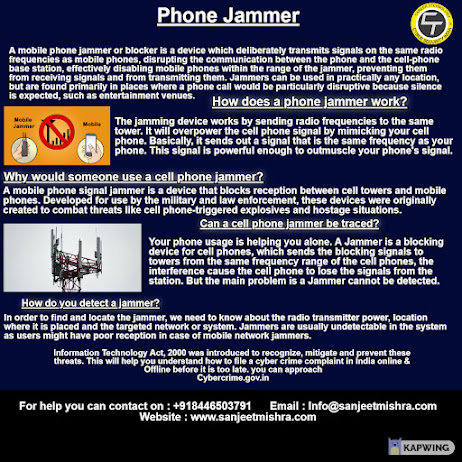
Phone Jammer A mobile phone jammer or blocker is a device which deliberately transmits signals on the same radio frequencies as mobile phones, disrupting the communication between the phone and the cell-phone, base station, effectively disabling mobile phones within the range of the jammer, preventing them from receiving signals and from transmitting them. Jammers can be used in practically any location, but are found primarily in places where a phone call would be particularly disruptive because silence is expected, such as entertainment venues. How does a phone jammer work? Mobile Jammer Mobile The jamming device works by sending radio frequencies to the same tower. It will overpower the cell phone signal by mimicking your cell phone. Basically, it sends out a signal that is the same frequency as your phone. This signal is powerful enough to outmuscle your phone's signal. Why would someone use a cell phone jammer? A mobile phone signal jammer is a device that blocks reception bet...
